Root any Android device and Make your own hacking device.
Enabling Superuser access on an Android device involves several steps, and the process can vary slightly depending on the device and Android version you are using. Here are the general steps to enable Superuser access:
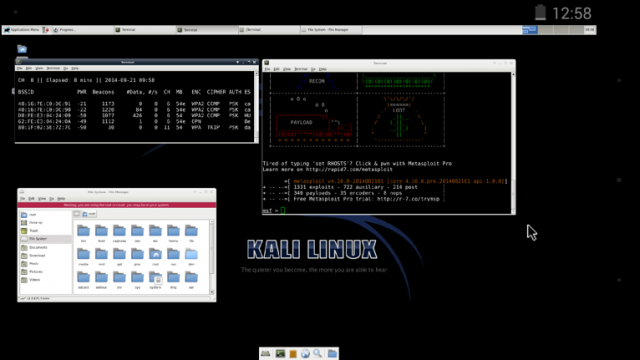
Root your Android device: In order to enable Superuser access, you must first root your Android device. Rooting involves unlocking the device's bootloader and installing a custom recovery that allows you to flash custom ROMs and gain access to the device's system files. The process for rooting your device can vary depending on the device and Android version you are using, and there are many online resources that can provide detailed instructions on how to root your device.
Install a Superuser app: Once you have rooted your device, you will need to install a Superuser app. This app will manage Superuser access and grant or deny permission requests from other apps. There are many Superuser apps available in the Google Play Store, including SuperSU and Magisk.
Grant Superuser access: After installing a Superuser app, you will need to grant Superuser access to individual apps that request it. When an app requests Superuser access, the Superuser app will display a prompt asking you to grant or deny permission. You can choose to grant permission permanently or just for the current session.
Manage Superuser access: It's important to manage Superuser access carefully to ensure that your device remains secure. Be sure to only grant Superuser access to apps that you trust, and revoke access for apps that no longer need it. You should also be careful when granting permanent access, as this can give an app unrestricted access to your device's system files.
In summary, enabling Superuser access on an Android device involves rooting the device, installing a Superuser app, and carefully managing access to ensure that your device remains secure. The process can be complex and should only be attempted by advanced users who understand the risks involved