Ethical Hacking - Sniffing
Sniffing is the process of monitoring and capturing all the packets passing through a given network using sniffing tools. This is a form of "phone tapping of the stars" and get to know about the conversation. It is also called wiretapping applied to the computer network.
There is a possibility that if a set of enterprise switch port is open, one employee of them can smuggle the entire traffic of the network. Anyone can plug in the network using the Ethernet cable in the same physical location or connect to the network with wireless and smell the total traffic.
In other words, by sniffing you can see both protected and unsafe traffic. In the right circumstances and with the right protocol, an attacking party may be able to collect information that may lead to further attacks or other issues for the network or system owner.
What can be sniffed?
One can sniff the following sensitive information from a network -
*Email Traffic
*FTP password
*Web traffic
*Telnet password
*Router configuration
*Chat session
*DNS traffic
*how it works
A sniffer normally converts the system's NIC into promisse mode so that it can listen to all the data transmitted over its segment.
The key mode refers to the unique method of Ethernet hardware, in particular, the Network Interface Card (NIC), which allows NIC to get all traffic on the network, even if this NIC is not addressed. By default, an NIC ignores all traffic that does not address it, which is done by comparing the destination address of the Ethernet packet with the device's hardware address (a.k. MAC). Although it makes sense for networking, it makes it difficult to use network monitoring and analysis software to diagnose unnecessary mode connectivity issues or traffic accounting.
A sniffer can constantly monitor all the traffic on the computer through NIC, decoding the information recorded in the data packet.
Sniffing
Sniffing can either be active or inactive in nature.
Idle sniff
Inactive sniffing, traffic is closed, but it is not changed in any way. Passive sniffing allows only listening. It works with hub devices. On the Hub device, traffic is sent to all ports. In a network that uses the hub to add a system, you can see all host traffic on the network. Therefore, an attacker can easily capture the traffic passing.
The good news is that nowadays the hubs are almost obsolete. Most modern networks use the switch. Therefore, passive sniffing is not more effective.
Active sniffing
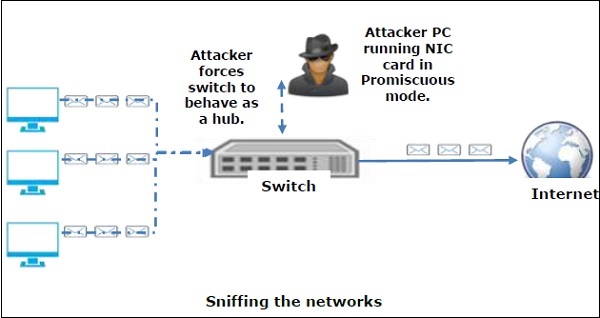
In active sniffing, traffic is not only locked and monitored, but it can be changed in some way as determined by the attack. Active sniffing is used to sniff the switch-based network. In this, the switch resolution addressable memory (CAM) table includes the address resolution packet (ARP) injected into a target network for flooding. CAM is connected to a port, keeps track of it.
The following are active sniffing techniques -
*Mac flood
*DHCP attacks
*DNS poison
*Spoofing attack
*Arp poison
*Protocols that are affected
*The tried and tested protocols like TCP / IP were never built keeping security in mind and therefore do not offer much resistance to potential intruders. Many rules lend easy sniffing -
HTTP - This is used to send information to clear text without any encryption and thus to actual target.
SMTP (Simple Mail Transfer Protocol) - SMTP is basically used in the transfer of email. This protocol is efficient, but sniffing does not include security.
NNTP (Network News Transfer Protocol) - It is used for all types of communications, but the main drawback is that data and even passwords are sent to the network in the form of clear text.
POP (Post Office Protocol) - POP is strictly used to get emails from servers. Sniffing in this protocol does not include protection because it can get stuck.
FTP (File Transfer Protocol) - FTP is used to send and receive files, but it does not offer any security features. All data is sent as clear text which can easily be sniffed.
IMAP (Internet Message Access Protocol) - IMAP is similar to SMTP in its functions, but it is highly vulnerable to sniffing.
Telnet - Telnet sends everything (username, password, keystrokes) to the network as clear text and therefore, it can easily be sniffed.
Sniffers are not dumb utilities that allow you to watch live traffic only. If you really want to analyze each packet, then save the capture and review it whenever the time is allowed.
Hardware Protocol Analyzer
Before we go into more details of sniffers, it is important that we discuss the hardware protocol analyzer. These devices plug in the network at the hardware level and can monitor traffic without any manipulation.
Used in monitoring and identifying malicious network traffic generated by the hacking software installed in the Hardware Protocol Analyzer system.
They capture a data packet, decode it, and analyze its contents according to some rules.
Hardware protocol analyzers allow attackers to see individual data bytes of each packet passing through the cable.
Due to their heavy cost in many cases these hardware tools are not easily available for most ethical hackers.
Valid interception
Legal Interception (LI) is defined as legally accepted access to communication network data such as telephone calls or email messages. LI should always be in the pursuit of a valid authority for the purpose of analysis or evidence. Therefore, LI is a security process in which a network operator or service provider allows law enforcement officials to use private communications of individuals or organizations.
Almost all countries have drafted and enacted the legislation to regulate law enforcement processes; Standardization groups are making the LI Technology specification. Typically, LI activities are taken for the purpose of security of infrastructure and cyber security. However, private network infrastructure operators can maintain LI capabilities as a built-in authority within their network, unless otherwise prohibited.
LI was previously known as wiretapping and has existed since the establishment of electronic communication.